Access Control & Audit Logs
73 products available
𝗪𝗵𝗮𝘁 𝗮𝗿𝗲 𝗔𝗰𝗰𝗲𝘀𝘀 𝗖𝗼𝗻𝘁𝗿𝗼𝗹 & 𝗔𝘂𝗱𝗶𝘁 𝗟𝗼𝗴𝘀?
Access Control and Audit Logs are essential components of modern security systems used by businesses to manage who can access specific resources within their facilities. Access Control refers to the mechanisms that are employed to regulate who can enter or use particular areas, systems, or data. Audit Logs, on the other hand, are records that track and document the actions taken by users, providing a trail of who accessed what and when. Together, these tools help organizations maintain security, enhance accountability, and comply with regulatory requirements.
These systems find primary applications in various business environments, including corporate offices, manufacturing plants, and data centers. They are crucial for safeguarding sensitive information and ensuring that only authorized personnel have access to critical areas or data. The ability to monitor and review access events through audit logs also allows companies to detect unauthorized access attempts and respond effectively to potential security breaches. As industries increasingly prioritize security, the relevance of Access Control and Audit Logs continues to grow, making them vital investments for businesses aiming to protect their assets.
𝗞𝗲𝘆 𝗙𝗲𝗮𝘁𝘂𝗿𝗲𝘀 𝗮𝗻𝗱 𝗦𝗽𝗲𝗰𝗶𝗳𝗶𝗰𝗮𝘁𝗶𝗼𝗻𝘀
Access Control and Audit Logs come with a variety of features and specifications that ensure robust security and usability. These specifications provide buyers with the necessary information to assess which solution best fits their needs.
Key specifications include:
1. Access Control Method
- Types include biometric, card-based, and keypad entry systems.
- Each method varies in terms of security level and user convenience.
2. Audit Log Capacity
- Indicates the volume of access events that can be stored.
- Common ranges can accommodate thousands to millions of entries depending on system capacity.
3. Data Encryption Standards
- Utilizes industry-standard encryption protocols to protect data integrity.
- AES and TLS are commonly used for secure data transmission.
4. User Interface
- Offers intuitive dashboards for easy monitoring and management of access controls.
- Features may include alert notifications and real-time reporting.
5. Integration Capabilities
- Compatibility with existing security systems and third-party applications.
- Supports integration with CCTV, alarms, and building management systems.
6. Compliance Features
- Built to adhere to various industry regulations and standards.
- Helps organizations maintain compliance with data protection laws.
7. Remote Access Management
- Allows administrators to manage access controls remotely through secure web portals.
- Facilitates quick adjustments to user permissions as needed.
8. Multi-Factor Authentication
- Enhances security by requiring users to provide multiple forms of verification.
- Common methods include a combination of passwords, tokens, or biometric data.
In summary, these specifications help organizations evaluate the security features, usability, and compliance of Access Control and Audit Logs, ensuring they select a solution that meets their specific needs.
𝗖𝗼𝗺𝗺𝗼𝗻 𝗔𝗽𝗽𝗹𝗶𝗰𝗮𝘁𝗶𝗼𝗻𝘀 𝗮𝗻𝗱 𝗨𝘀𝗲 𝗖𝗮𝘀𝗲𝘀
Access Control and Audit Logs serve various industries, providing tailored security solutions based on their unique requirements.
1. Corporate Offices: These systems are used to restrict access to sensitive areas such as executive offices or server rooms, ensuring that only authorized personnel can enter.
2. Manufacturing Facilities: Access control is critical to safeguard machinery and restricted zones, preventing unauthorized access that could lead to safety hazards or theft.
3. Data Centers: With the high value of data, these facilities implement stringent access controls to protect servers and sensitive information, logging all access attempts for audits.
4. Healthcare Institutions: Hospitals and clinics utilize access controls to restrict access to patient records and medication storage, ensuring compliance with health regulations.
5. Educational Institutions: Universities and schools deploy these systems to regulate access to dormitories and labs, enhancing security for students and staff.
6. Government Facilities: Public sector organizations implement access controls to protect sensitive areas and maintain national security, tracking all access events for compliance.
7. Retail Environments: Retailers use audit logs to monitor employee access to back-end systems, helping to prevent theft and ensure proper inventory management.
𝗣𝗿𝗼𝗱𝘂𝗰𝘁 𝗩𝗮𝗿𝗶𝗮𝗻𝘁𝘀 𝗮𝗻𝗱 𝗦𝘂𝗯𝗰𝗮𝘁𝗲𝗴𝗼𝗿𝗶𝗲𝘀
Access Control and Audit Logs come in various forms, tailored to meet specific business needs. Each variant offers unique features and capabilities.
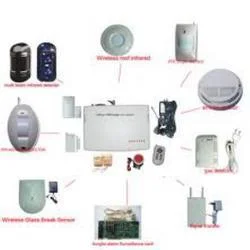
Card-Based Access Control Systems: These systems utilize RFID cards or key fobs to grant access. They are easy to implement and can be cost-effective for businesses looking to manage entry points simply.
Biometric Access Control Systems: These advanced systems use fingerprint, facial recognition, or iris scanning technology for authentication. They provide a high level of security and reduce the risk of unauthorized access.
Cloud-Based Access Control Solutions: These systems leverage cloud technology to provide remote management capabilities. They allow users to control access points from anywhere, making them ideal for businesses with multiple locations.
Mobile Access Control Systems: These solutions enable users to access secured areas using their smartphones. This convenience is increasingly popular in modern workplaces, offering flexibility and ease of use.
𝗕𝗲𝗻𝗲𝗳𝗶𝘁𝘀 𝗮𝗻𝗱 𝗔𝗱𝘃𝗮𝗻𝘁𝗮𝗴𝗲𝘀
Investing in Access Control and Audit Logs presents numerous advantages for businesses looking to enhance security and operational efficiency.
Key benefits include:
1. Enhanced Security: These systems protect sensitive areas and information, reducing the risk of unauthorized access and potential data breaches.
2. Improved Accountability: Audit logs provide a clear record of access events, allowing organizations to track who accessed what information and when, fostering greater accountability among employees.
3. Regulatory Compliance: Many industries face strict regulatory requirements regarding data protection. Access Control and Audit Logs help organizations meet these compliance standards.
4. Customizable Solutions: Businesses can tailor access control systems to meet their specific needs, allowing for flexibility in security measures based on changing requirements.
5. Increased Operational Efficiency: Streamlined access processes can lead to improved workflow and reduced delays, as employees can access necessary areas without hindrance.
6. Real-Time Monitoring: Many systems allow for real-time monitoring of access attempts, enabling quick responses to potential security threats.
𝗕𝘂𝘆𝗶𝗻𝗴 𝗚𝘂𝗶𝗱𝗲 𝗳𝗼𝗿 𝗕𝟮𝗕 𝗕𝘂𝘆𝗲𝗿𝘀
When sourcing Access Control and Audit Logs, buyers should consider several key factors to ensure they select the right solution for their organization.
1. Quality Assessment: Evaluate the quality of the systems by checking reviews, testimonials, and case studies. Look for systems that have a proven track record in similar industries.
2. Supplier Verification: Conduct thorough research to vet suppliers. Ensure they have a solid reputation and offer reliable customer support and warranty options.
3. Pricing and MOQ: Analyze the pricing structure and be aware of minimum order quantities. Compare different suppliers to find the best value for your investment.
4. Delivery and Lead Times: Understand logistics and lead times for delivery. Ensure the supplier can meet your deadlines, especially if you require urgent implementation.
5. Compliance Requirements: Confirm that the solutions meet necessary regulatory standards relevant to your industry, such as ISO certifications or local compliance laws.
𝗖𝗼𝗺𝗽𝗹𝗶𝗮𝗻𝗰𝗲 𝗮𝗻𝗱 𝗖𝗲𝗿𝘁𝗶𝗳𝗶𝗰𝗮𝘁𝗶𝗼𝗻𝘀
Access Control and Audit Logs must adhere to various quality standards and certifications to ensure reliability and safety in their operations. Relevant quality standards include ISO 9001, which focuses on maintaining consistent quality management systems, ensuring that products meet customer and regulatory requirements.
Industry-specific certifications such as CE may also apply, indicating that the product meets EU safety and health standards. Safety and testing requirements ensure that the systems are rigorously evaluated for performance and security vulnerabilities.
Additionally, regional compliance considerations are vital, as different areas may have specific regulations governing access control systems. Buyers should confirm that their chosen solution complies with local laws, ensuring they avoid potential fines or legal complications.
𝗪𝗵𝘆 𝗦𝗼𝘂𝗿𝗰𝗲 𝗔𝗰𝗰𝗲𝘀𝘀 𝗖𝗼𝗻𝘁𝗿𝗼𝗹 & 𝗔𝘂𝗱𝗶𝘁 𝗟𝗼𝗴𝘀 𝗳𝗿𝗼𝗺 𝗣𝗲𝗽𝗮𝗴𝗼𝗿𝗮?
Pepagora offers a trusted platform for sourcing Access Control and Audit Logs, providing several key advantages to businesses.
Verified Supplier Network: Pepagora has established a rigorous verification process for suppliers, ensuring that buyers can trust the quality and reliability of the products they purchase.
Streamlined RFQ Process: The platform simplifies the request for quotation (RFQ) process, allowing businesses to quickly obtain competitive quotes from multiple suppliers, making it easier to compare options.
Trade Assurance and Support: Pepagora offers trade assurance, protecting buyers during transactions and providing support to address any concerns or issues that may arise.
Regional Coverage: With a strong presence in India, the GCC, and Southeast Asia, Pepagora ensures that businesses across these regions can access a wide range of quality products tailored to their specific security needs.
Newly Added
Recently Added
Chorghade Power Solutions
Advanced Time Attendance System Secure Access Control Real Time Reporting
Industrial High Resolution Weatherproof CCTV Cameras for Surveillance
Intrusion Systems Advanced Detection Durable Construction Security
Comtel Communications, Delhi
Professional Access Control Systems For Security Management
Professional Audio Video Conferencing Systems For Seamless Remote Meetings
Building Management System For Commercial Industrial HVAC Lighting Security
Capricorn Security Solutions
Business Security CCTV Surveillance Systems With Remote Monitoring
Business Security DVR Standalone High Quality Recording No Monthly Fees
Professional H.264 T2 DVR For Business Security With Remote Monitoring
Benz Security & Fire Technologies
Secure Access Control Systems For Facilities Management And Safety
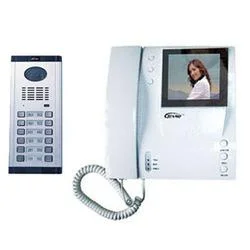
Multi Apartment Video Door Phone System HD Video Two Way Audio
Wireless Video Capsule Endoscopy For Gastrointestinal Diagnostics
A. D. Brass Emporium
Premium Retractable Belt Queue Managers For Crowd Control
Wall Mounted Queue Manager for Banks Hospitals Offices Durable Reliable
Industrial Brass Fittings For Plumbing Hydraulic Systems Durable Leak Proof
Ace Securities
Commercial Industrial Fire Alarm Systems Premium Detection Safety
Solar Water Heaters High Efficiency 5 Year Warranty
Commercial Security CCTV Camera HD Surveillance Remote Monitoring Weatherproof
Shree laxmi Narasimmar Electronics
Professional Wired And Wireless Security System With 12 Zone Expandability
Security System Blackcat Z Plus LED Alarm RF Transmission Backup Power
Commercial Security System Blackcat Z Plus LCD Microcontroller 4/8 Zone
Mi - Tech System
Access Control Systems With Biometric Card PIN Security
Home Security Systems with Alarms, Sensors, and Detectors
Commercial Fire Alarm Systems Premium Industrial Safety Reliable
A. B. Machine Tools
Industrial Pipe Cutting Machines For Metalworking And Construction
Healthcare Automation Control Solutions For Precision Medical Devices
Hiwin Precision Ball Screws For Industrial Automation And CNC
Astra Group Of Company Pvt Ltd
Commercial CCTV Cameras HD IP Dome Bullet PTZ Night Vision
Business Security IP CCTV Cameras High Resolution Night Vision Remote Access
Security IP Safety Cameras HD Surveillance Night Vision Remote Access
Why Businesses Trust Pepagora
Thousands of companies trust Pepagora to source smarter and sell faster
Expand Your Sales Globally
25000+Products listed.Get discovered by global buyers
Tools to boost visibility
Build your own catalog

Source Smarter,Grow Faster
4000+Active RFQs
100+ Countries served
Easy Sourcing Tools