Similar Products
Description
Advanced Multi Door Controllers serve as the intelligent core of comprehensive access management systems, offering centralized command over numerous entry points within a single fa...
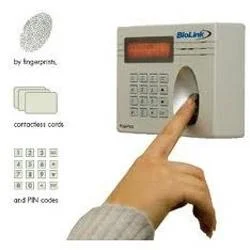
Advanced Multi Door Controllers serve as the intelligent core of comprehensive access management systems, offering centralized command over numerous entry points within a single facility or campus. These robust devices empower organizations to maintain stringent security oversight while simplifying access administration across their entire premises. Built for durability and adaptability, they support a wide array of authentication methods, including proximity cards, PIN codes, and biometric verification. The system's architecture allows for effortless integration with existing security infrastructure, making it an ideal solution for enhancing or scaling security capabilities without the need for a complete system overhaul. This approach provides a future-proof foundation for evolving security requirements. These controllers are indispensable across industries where precise access management is critical. Corporate offices deploy them to regulate employee movement between departments, secure executive suites, and protect sensitive data rooms while maintaining detailed access logs. Manufacturing facilities rely on them to manage entry to production areas, quality control labs, and inventory storage. Educational campuses use them to control access to dormitories, research labs, and administrative centers, enhancing overall safety. Healthcare institutions depend on them to secure areas containing patient records, medications, and diagnostic equipment. Technology parks and data centers implement them to safeguard server rooms, network operations centers, and other critical infrastructure from unauthorized entry. The value proposition extends beyond basic security to include operational efficiency and regulatory adherence. These systems provide dependable 24/7 performance with built-in fail-safe protocols and backup power support, ensuring continuous security coverage during outages or system events. The flexible configuration allows for tailoring access rules, time schedules, and user permissions to match specific operational workflows and security policies. Organizations benefit from reduced administrative overhead through centralized management and automated enforcement of access protocols. Furthermore, the systems generate comprehensive audit trails and detailed access reports, which are crucial for demonstrating compliance with various industry regulations and security standards, providing verifiable documentation of all access control activities. Key Features: - Centralized management platform for controlling multiple access points from a single interface. - Support for diverse authentication methods including cards, PIN codes, and biometric scanners. - Highly flexible configuration for creating custom access rules, time zones, and user permissions. - Integrated backup power support and fail-safe mechanisms to ensure continuous, uninterrupted operation. - Seamless integration capability with existing security systems, alarms, and monitoring software. Benefits: - Strengthened security through centralized oversight and control of all facility access points. - Operational flexibility offered by multiple, configurable authentication options to suit different needs. - Tailored security protocols that adapt precisely to your organization's specific requirements and workflows. - Guaranteed operational continuity, maintaining security integrity during power or system interruptions. - Simplified implementation and scalability through easy integration with current infrastructure, reducing complexity and cost.
Specifications
| Additional Information | |
|---|---|
| Country of Origin | India |
| Customisable | No |
Application
These advanced multi door controllers deliver centralized command for modern access systems, efficiently managing multiple entry points from a single, intuitive interface. Designed for medium to large-scale facilities, they coordinate access across various zones and departments, integrating smoothly with card readers, biometric scanners, and alarm systems to create a unified security network. Engineered for demanding operational environments, the controllers support numerous authentication protocols while guaranteeing consistent reliability. Organizations gain from adaptable configurations that evolve with changing security policies and access demands. The system ensures non-stop protection through integrated backup power and fail-safe mechanisms, delivering uninterrupted security during critical events and power disruptions. - Office complexes regulating staff access across multiple floors, departments, and restricted zones. - Data centers and server farms securing critical infrastructure, network hubs, and equipment rooms. - Manufacturing and industrial plants controlling entry to production floors, warehouses, and hazardous material storage. - Educational institutions monitoring access to classrooms, laboratories, libraries, and administrative offices. - Healthcare facilities securing patient record archives, pharmacies, laboratories, and specialized treatment areas.
Trade Details
| Available Stock | In stock |
| Sample Availability | No |
Payment Terms
| Payment Terms |
|
Company Profile

Anglo Swiss Watch Co., Kolkata, West Bengal
Trading CompanyDistributor / Wholesaler
Factory Details
Factory SizeBelow 1000 sqm
Annual Production Capacity0
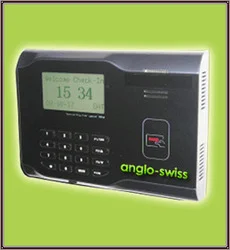
Secure Access Management Advanced Multi Door Controllers For Offices
Secure Access Management Advanced Multi Door Controllers provide centralized control for offices, data centers, and industrial facilities with flexible configuration and reliable performance for diverse security needs.
Min. Order Quantity: 1 units
Shipping
Shipping fee and delivery date to be negotiated. Contact supplier now for more details.
Anglo Swiss Watch Co., Kolkata
Trading Company